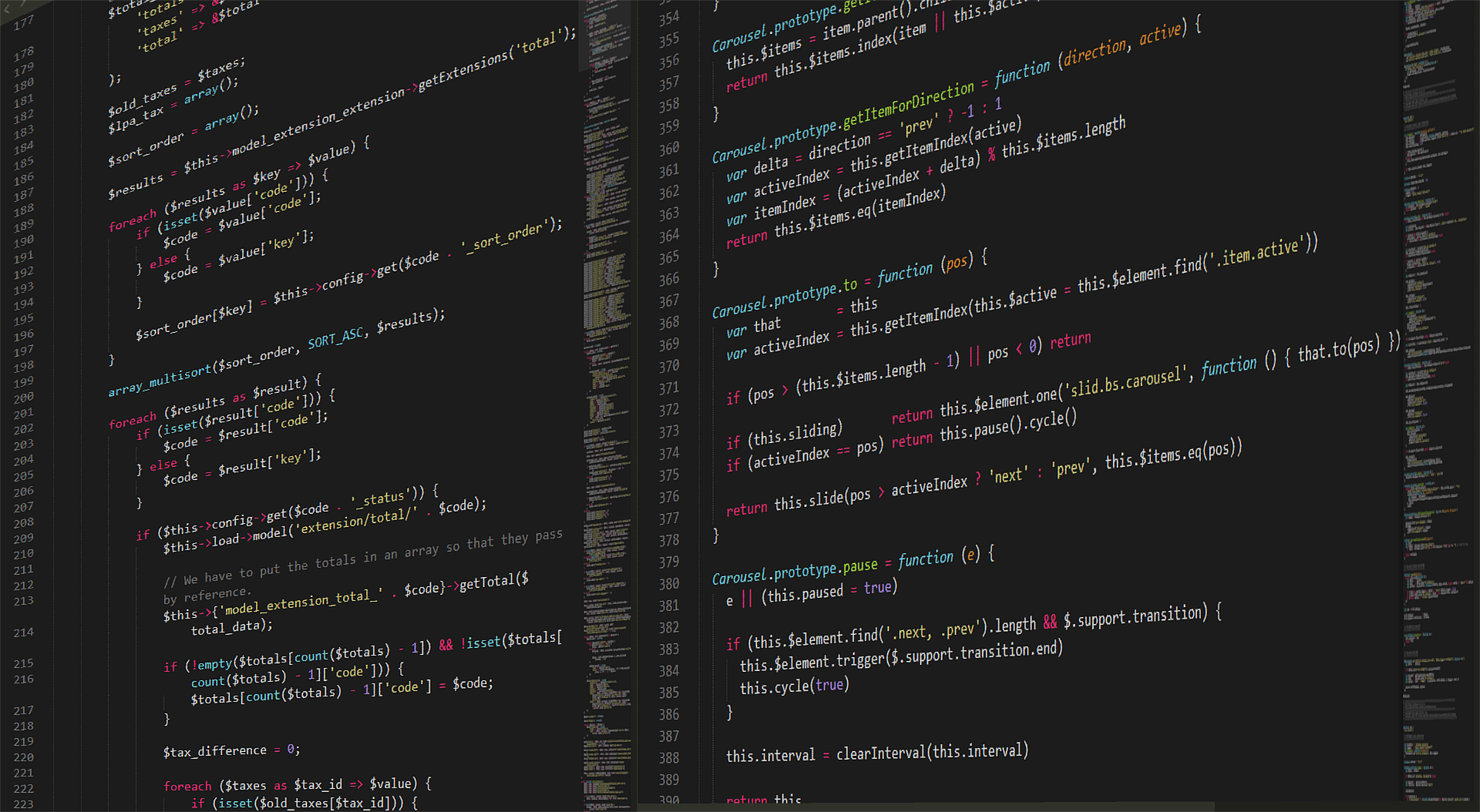
Top 8 Metrics to Collect During a Red Team Test
Why should we collect metrics in a red team test? Metrics are a valuable way [...]
“Shark on the Router” (Authentication Bypass in Wireless Router Chipsets)
Multiple wireless router chipsets were discovered to be vulnerable to authentication bypass, giving a threat [...]
BLE Vulnerability Leads to Broken Authentication and Malicious Data Transfer
A successful Bluetooth Low Energy Spoofing Attack (BLESA) allows threat actors to connect with a [...]
What to Include in Your Security Testing Supplier’s Agreement
A successful penetration test requires good preparation with an airtight service-level contract between the customer [...]
Cyber Security After COVID-19: How to Protect Your Business
What is cyber security after COVID-19? We have now passed the stage of emergency policies [...]
Top Security Breaches that have Zoomed into 2020 Thus Far
We have all seen how fast things can change in 2020 but the one thing [...]
File Manager Plugin in WordPress Contains a Remote Code Execution Vulnerability
WordPress’ popular plugin File Manager (versions 6.0-6.8) contains a vulnerability that allows an attacker to [...]
The Importance of Minimising Your Attack Surface
With every security test, Risk Crew has performed, there has been at least one attack [...]
Multiple Vulnerabilities found in Microsoft Azure Sphere
Microsoft Azure Sphere versions 20.07 and 20.06 contain vulnerabilities such as remote code execution and [...]
5 Items to Consider When Choosing a Pen Test Provider
As security professionals with nearly two decades in the industry, we understand the significance of [...]